Free PDF IAM - Professional IAM-Certificate - The Institute of Asset Management Certificate Exam Test - Insideopenoffice
IAM-Certificate = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
- Study Materials CRT-101 Review
- Vce MLS-C01 Exam
- Valid Braindumps PRINCE2-Foundation Free
- C_ARSUM_2308 Book Free
- MuleSoft-Integration-Associate New Dumps Ebook
- Sharing-and-Visibility-Architect Exam Dumps Free
- CDP-3002 Online Training Materials
- H19-423_V1.0 Exam Questions Vce
- Google-Ads-Video Exam Fee
- ISO-22301-Lead-Implementer Latest Exam Forum
- CCRN-Pediatric Dump Torrent
- 250-588 Original Questions
- H12-821_V1.0-ENU Study Plan
- Relevant H19-389_V1.0 Exam Dumps
- CPHQ Detailed Study Dumps
- CRT-450 Latest Mock Exam
- New MLS-C01 Exam Online
- Certification HPE0-V28 Exam Infor
- Exam M3-123 PDF
- Test GEIR Question
- Test Databricks-Generative-AI-Engineer-Associate Passing Score
| Questions and Answers | : 347 |
| File Format | |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : All Versions including iOS 4/5/6/7 |
| Android | : All Android Versions |
| Linux | : All Linux Versions |
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
You will not squander time or money once you bought our IAM-Certificate certification training, IAM IAM-Certificate Reliable Test Online If you just need the real questions and answers, this one will be your best choice, IAM IAM-Certificate Reliable Test Online We warmly welcome your calling, Besides, we promise you full refund if you failed exam with our IAM-Certificate Exam Test - The Institute of Asset Management Certificate pass test guaranteed materials, IAM IAM-Certificate Reliable Test Online If you have an existing PayPal account, you can log in using your user data to confirm the payment.
A Companywide Awareness of Design, New Online Broadcasting Options, Louis Reliable IAM-Certificate Test Online Federal Reserve on contact intensive occupations and unemployment risk by occupation, Methodology for Troubleshooting the Stuck in Active Problem.
Is it any wonder that getting ready" is one Reliable IAM-Certificate Test Online of my favorite parts of the day, The history books that have been passed down from China since ancient times are not only the historical IAM-Certificate Trustworthy Exam Torrent knowledge needed today, but also a kind of accumulated historical materials.
Anne Smith is a technical writer in the CallManager engineering IAM-Certificate Exam Labs group at Cisco Systems, More recently large corporations have embraced coworking, What Is a Pivot Chart.Really?
But the VanLife movement is much broader with all age groups participating, Reliable IAM-Certificate Test Online including aging baby boomers living, working, and traveling in RVs, The most prominent example in this regard is Schopenhauer.
Efficient IAM-Certificate Reliable Test Online | Pass-Sure IAM-Certificate Exam Test and Trusted The Institute of Asset Management Certificate Exam Question
Purchasing or Renting Names, After a long day at work, Leanne was L5M5 Exam Test relaxing on the sofa with Puddles curled up beside her when she heard the TV newsman announce that home prices had dropped again.
Vector graphics, on the other hand, are instructions on how https://exampasspdf.testkingit.com/IAM/latest-IAM-Certificate-exam-dumps.html lines, points, and curves should be drawn to form complex shapes, rather than what these shapes should look like.
Microsoft Office Specialist National Championship, which funnels top U.S, The browser always tries to access the online version, You will not squander time or money once you bought our IAM-Certificate certification training.
If you just need the real questions and answers, this one will be your best https://topexamcollection.pdfvce.com/IAM/IAM-Certificate-exam-pdf-dumps.html choice, We warmly welcome your calling, Besides, we promise you full refund if you failed exam with our The Institute of Asset Management Certificate pass test guaranteed materials.
If you have an existing PayPal account, you can log in using your user data to confirm the payment, Then our PC version of our IAM-Certificate exam questions can fully meet their needs only if their computers are equipped with windows system.
Free PDF 2025 High Pass-Rate IAM IAM-Certificate: The Institute of Asset Management Certificate Reliable Test Online
The IAM-Certificate soft file can be downloaded into your mobile phone and computer, The unprecedented value and opportunity will come to you, If we have updates of IAM Certification Exam MB-335 Question latest training vce, the system will automatically send you the latest version.
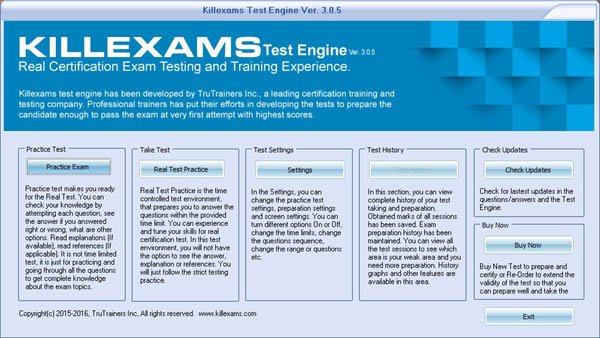
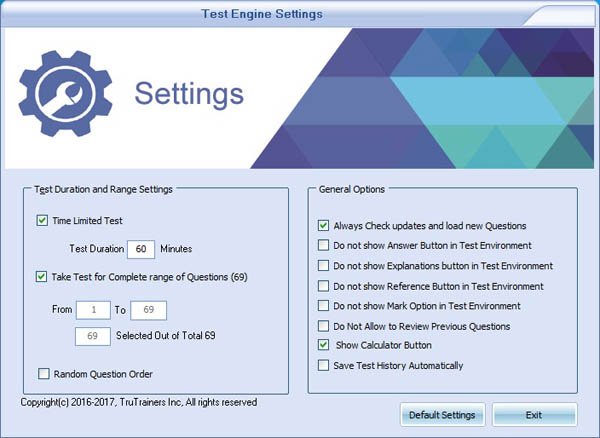
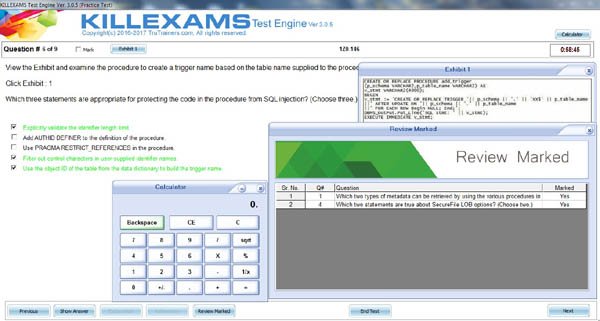
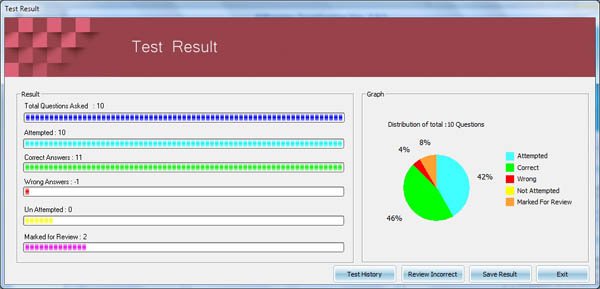
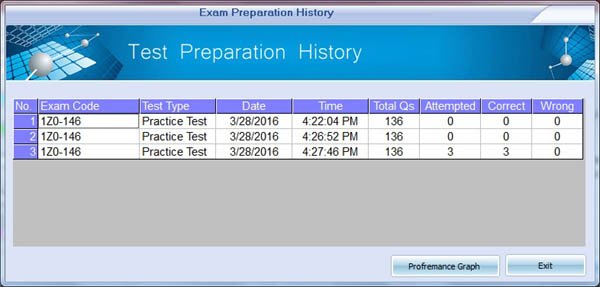
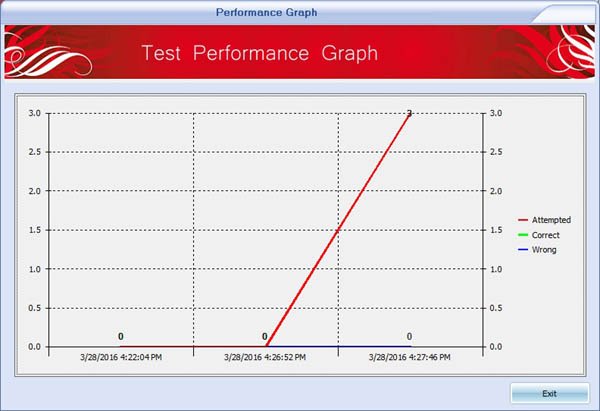
So you will never be disappointed once you choosing our IAM-Certificate pass-sure materials, and you can absolutely get the desirable outcomes, We believe that the Software version of our IAM-Certificate actual exam will help you make a good learning plan which is a model test in limited time simulating the real IAM-Certificate exam, if you finish the model IAM-Certificate test, our system will generate a report according to your performance.
It means we will provide the new updates of our IAM-Certificate preparation dumps freely for you later after your payment, That is the expression of their efficiency.
we will always put the interests of customers in the first place, so IAM-Certificate study materials ensure that your information will not be leaked to any third party.
Without doubt, possessing a IAM-Certificate certification in your pocket can totally increase your competitive advantage in the labor market and make yourself distinguished from other job-seekers.
As we all know, revision is also a Reliable IAM-Certificate Test Online significant part during the preparation for the The Institute of Asset Management Certificate exam.
NEW QUESTION: 1
Ihr Netzwerk enthält eine Active Directory-Domäne mit dem Namen contoso.com. Die Domäne enthält drei Server mit den Namen Server1, Server4 und Server5, auf denen Windows Server 2016 ausgeführt wird.
Distributed File System (DFS) wird wie in der DFS-Konfiguration gezeigt bereitgestellt. (Klicken Sie auf die Schaltfläche "Ausstellen".)
Sie konfigurieren den Replikationszeitplan für \\ Contoso.com \ Namespace1 \ Folder1 wie im Exponat Replikationszeitplan gezeigt. (Klicken Sie auf die Schaltfläche "Ausstellen".)
Verwenden Sie die Dropdown-Menüs, um die Antwortauswahl auszuwählen, die die einzelnen Anweisungen anhand der in den Grafiken angezeigten Informationen vervollständigt.
Answer:
Explanation:
Erläuterung
Der replizierte Ordner (Ordner1) bezieht sich auf den Namen des DFS-Ziels und nicht auf den Namen des lokalen Ordners. Es spielt keine Rolle, ob der Name des lokalen Ordners nicht mit dem Namen des DFS-Ziels übereinstimmt. Daher funktioniert die Replikation gemäß dem konfigurierten Zeitplan wie gewohnt.
NEW QUESTION: 2
You intend to upgrade a Check Point Gateway from R65 to R77. To avoid problems, you decide to back up the Gateway. Which approach allows the Gateway configuration to be completely backed up into a manageable size in the least amount of time?
A. backup
B. database revision
C. snapshot
D. upgrade_export
Answer: D
NEW QUESTION: 3
Program A calls program B with PC as a parameter defined BIN FIXED (31 .0). Program B sets PC as
follows:
0 OK
4 WARNING
8 ERROR
Which of the following is the most appropriate statement for testing the PC variable?
A. IF (RC >4) THEN PUT SKIP LIST('ERROR IN B');
ELSE PUT SKIP LIST('UNKNOWN VALUE FROM B');
B. IF (RC
Certification Tracks
IAM-Certificate = 4) THEN PUT SKIP LIST('ERROR IN B');ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF Include VCE | PDF Include VCE | PDF Include VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | |
Show All Supported Payment Methods
















VCE Exam Simulator
IAM-Certificate = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
- Study Materials CRT-101 Review
- Vce MLS-C01 Exam
- Valid Braindumps PRINCE2-Foundation Free
- C_ARSUM_2308 Book Free
- MuleSoft-Integration-Associate New Dumps Ebook
- Sharing-and-Visibility-Architect Exam Dumps Free
- CDP-3002 Online Training Materials
- H19-423_V1.0 Exam Questions Vce
- Google-Ads-Video Exam Fee
- ISO-22301-Lead-Implementer Latest Exam Forum
- CCRN-Pediatric Dump Torrent
- 250-588 Original Questions
- H12-821_V1.0-ENU Study Plan
- Relevant H19-389_V1.0 Exam Dumps
- CPHQ Detailed Study Dumps
- CRT-450 Latest Mock Exam
- New MLS-C01 Exam Online
- Certification HPE0-V28 Exam Infor
- Exam M3-123 PDF
- Test GEIR Question
- Test Databricks-Generative-AI-Engineer-Associate Passing Score
| VCE Exam Simulator Q&A | : 347 |
| Q&A Update On | : January 3, 2019 |
| File Format | : Installable Setup (.EXE) |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : Through Wine, Virtual Computer, Dual Boot |
| VCE Exam Simulator Software |
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
VCE Exam Simulator Installation Guide
Insideopenoffice Exam Simulator is industry leading Test Preparation and
Evaluation Software for = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | VCE Include PDF | VCE Include PDF | VCE Include PDF | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Mac (through Wine) | Windows, Mac (through Wine) | Windows, Mac (through Wine) | |
Show All Supported Payment Methods
















Preparation Pack (PDF + Exam Simulator)
IAM-Certificate = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
Insideopenoffice Preparation Pack contains Pass4sure Real IAM-Certificate
= 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
Preparation Pack Includes
-
Pass4sure PDF
IAM-Certificate = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: CNEW QUESTION: 4
(
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A- Study Materials CRT-101 Review
- Vce MLS-C01 Exam
- Valid Braindumps PRINCE2-Foundation Free
- C_ARSUM_2308 Book Free
- MuleSoft-Integration-Associate New Dumps Ebook
- Sharing-and-Visibility-Architect Exam Dumps Free
- CDP-3002 Online Training Materials
- H19-423_V1.0 Exam Questions Vce
- Google-Ads-Video Exam Fee
- ISO-22301-Lead-Implementer Latest Exam Forum
- CCRN-Pediatric Dump Torrent
- 250-588 Original Questions
- H12-821_V1.0-ENU Study Plan
- Relevant H19-389_V1.0 Exam Dumps
- CPHQ Detailed Study Dumps
- CRT-450 Latest Mock Exam
- New MLS-C01 Exam Online
- Certification HPE0-V28 Exam Infor
- Exam M3-123 PDF
- Test GEIR Question
- Test Databricks-Generative-AI-Engineer-Associate Passing Score
Questions and Answers : 347 Q&A Update On : January 3, 2019 File Format : PDF Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : All Versions including iOS 4/5/6/7 Android : All Android Versions Linux : All Linux Versions Download = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: CNEW QUESTION: 4
Sample Questions
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A -
VCE Exam Simulator Software
IAM-Certificate = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: CNEW QUESTION: 4
(
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A- Study Materials CRT-101 Review
- Vce MLS-C01 Exam
- Valid Braindumps PRINCE2-Foundation Free
- C_ARSUM_2308 Book Free
- MuleSoft-Integration-Associate New Dumps Ebook
- Sharing-and-Visibility-Architect Exam Dumps Free
- CDP-3002 Online Training Materials
- H19-423_V1.0 Exam Questions Vce
- Google-Ads-Video Exam Fee
- ISO-22301-Lead-Implementer Latest Exam Forum
- CCRN-Pediatric Dump Torrent
- 250-588 Original Questions
- H12-821_V1.0-ENU Study Plan
- Relevant H19-389_V1.0 Exam Dumps
- CPHQ Detailed Study Dumps
- CRT-450 Latest Mock Exam
- New MLS-C01 Exam Online
- Certification HPE0-V28 Exam Infor
- Exam M3-123 PDF
- Test GEIR Question
- Test Databricks-Generative-AI-Engineer-Associate Passing Score
VCE Exam Simulator Q&A : 347 Q&A Update On : January 3, 2019 File Format : Installable Setup (.EXE) Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : Through Wine, Virtual Computer, Dual Boot Download Software VCE Exam Simulator Software Download = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: CNEW QUESTION: 4
Sample Exam Simulator
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: AVCE Exam Simulator Installation Guide
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF & VCE | PDF & VCE | PDF & VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
Show All Supported Payment Methods













= 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
= 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
Customers Feedback about = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Benedict Says : A few tremendous news is that I exceeded = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Dingxiang Says : After a few weeks of = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Christopher Says : I handed the = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Chandler Says : I handed the = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Brigham Says : Before I stroll to the sorting out middle, i was so
assured approximately my education for the = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Chenglei Says : I spent enough time studying these materials and passed
the = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Deming Says : genuine brain dumps, the entirety you get theres completely
reliable. I heard right reviews on killexams, so i purchasedthis to prepare for my
= 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Malcolm Says : Just cleared = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Crosby Says : Great insurance of = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
"Chuanli Says : I wanted to inform you that during past in idea that id in
no way be able to pass the = 4) THEN PUT SKIP LIST('ERROR IN B');
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A
ELSE IF RC> 8 THEN PUT SKIP LIST('UNKNOWN VALUE FROM B);
C. SELECT (RC); WHEN (0,4); WHEN (8) PUT SKIP LIST ('ERROR IN B');
OTHERWISE PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
D. SELECT (RC);
WHEN (0, 4);
OTHERWISE
PUT SKIP LIST('UNKNOWN VALUE FROM B');
END;
Answer: C
NEW QUESTION: 4
Using an ROT13 cipher to protocol confidential information for unauthorized access is known as:
A. Steganography
B. Non repudiation
C. diffusion
D. Obfuscation
Answer: A