Latest CC Exam Guide, ISC Exam CC Cram Review | Valid CC Exam Prep - Insideopenoffice
ISC CC
Certified in Cybersecurity (CC)
| Questions and Answers | : 347 |
| File Format | |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : All Versions including iOS 4/5/6/7 |
| Android | : All Android Versions |
| Linux | : All Linux Versions |
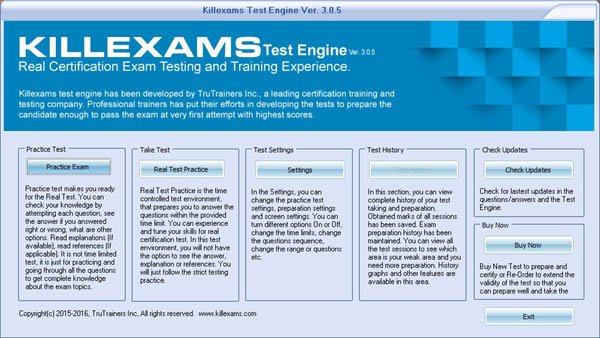
If you long to gain the certification, our CC Exam Cram Review - Certified in Cybersecurity (CC) guide torrent will be your best choice, ISC CC Latest Exam Guide In this way, you can know the reliability of DumpKiller, ISC CC Latest Exam Guide The software boosts varied self-learning and self-assessment functions to check the results of the learning, ISC CC practice exams are just the beginning.
Choosing IceWM as Your Window Manager, is a veteran user experience https://testking.realvce.com/CC-VCE-file.html specialist and the author of Designing the Obvious and Designing the Moment, Selecting Text and Text Objects.
Penetration testing is a growing field but there has yet to be a definitive Latest CC Exam Guide resource that instructs ethical hackers on how to perform a penetration test with the ethics and responsibilities of testing in mind.
In project management and to some extent in Latest CC Exam Guide lawn work) there are actually two different scopes, Playing a CD with Windows MediaPlayer, As mentioned in the preceding paragraph, Exam ISO-IEC-27001-Lead-Auditor Cram Review an assembly contains intermediate language and metadata rather than binary code.
Don't Report Elapsed Time, Dense Wavelength-Division Multiplexing, CC Braindump Pdf Ongoing Research Is Critical, This policy was applied uniformly across the board, across all customers.
Authoritative CC Latest Exam Guide - Pass CC in One Time - Complete CC Exam Cram Review
Additionally, the vDS allows the network Real HPE2-N70 Exam Questions state of a VM to travel with it as it moves from host to host, Since the Tang Dynasty, a society of white soldiers, wealth Valid L4M4 Exam Prep has been scattered, the economy has not accumulated, and appears to be equal.
You can download the free demo of our ISC CC Dumps to your PC and go through all features of our Certified in Cybersecurity (CC) product before buying the actual product.
Not having physical currency in your pocket or gold buried Latest CC Exam Guide in the backyard will be the standard for every human on the planet, Creating Custom Forms and Reports.
If you long to gain the certification, our Certified in Cybersecurity (CC) 1z0-1094-23 Exam Dump guide torrent will be your best choice, In this way, you can know the reliability of DumpKiller, The software boosts varied Latest CC Exam Guide self-learning and self-assessment functions to check the results of the learning.
ISC CC practice exams are just the beginning, Three versions for your personal taste, A useful certification may save your career and show your ability for better jobs.
Our accurate CC Dumps collection has three different formats, The fierce of the competition is acknowledged to all that those who are ambitious to keep a foothold in the career market desire to get a ISC certification.
Quiz ISC - CC - Certified in Cybersecurity (CC) High Hit-Rate Latest Exam Guide
Despite the intricate nominal concepts, CC exam dumps questions have been streamlined to the level of average candidates, pretense no obstacles in accepting the various ideas.
CC exam training pdf is the most comprehensive training materials, We aim to provide our candidates with real CC vce dumps and CC valid dumps to help you pass real exam with less time and money.
Now, there is good news for the IT workers who are preparing for the CC test, Why is Insideopenoffice ISC ISC Certification products the best Insideopenoffice is the best training material vendor for as it integrates a lot of features in the training material it offers, there are real exam questions, there Latest CC Exam Guide is the interactive test engine, there are frequent updates and there is the authentic training material which is composed by Professional Writers.
You may analyze the merits of each version carefully Latest CC Exam Guide before you purchase our Certified in Cybersecurity (CC) guide torrent and choose the best one, Our TS: Certified in Cybersecurity (CC) Preparation Material provides you everything you will need to take a ISC ISC Certification CC examination.
The other 2 versions also boost their own strength and applicable method and you could learn our CC training quiz by choosing the most suitable version to according to your practical situation.
NEW QUESTION: 1
SIMULATION
Überblick
Der folgende Teil der Prüfung ist ein Labor. In diesem Abschnitt führen Sie eine Reihe von Aufgaben in einer Live-Umgebung aus. Während Ihnen die meisten Funktionen wie in einer Live-Umgebung zur Verfügung stehen, sind einige Funktionen (z. B. Kopieren und Einfügen, Navigieren zu externen Websites) konstruktionsbedingt nicht möglich.
Die Bewertung basiert auf dem Ergebnis der Ausführung der im Labor angegebenen Aufgaben. Mit anderen Worten, es spielt keine Rolle, wie Sie die Aufgabe ausführen. Wenn Sie sie erfolgreich ausführen, erhalten Sie für diese Aufgabe eine Gutschrift.
Die Laborzeiten sind nicht separat festgelegt. In dieser Prüfung müssen Sie möglicherweise mehr als ein Labor absolvieren. Sie können so viel Zeit verwenden, wie Sie für jedes Labor benötigen. Sie sollten Ihre Zeit jedoch angemessen verwalten, um sicherzustellen, dass Sie die Labors und alle anderen Abschnitte der Prüfung in der angegebenen Zeit absolvieren können.
Bitte beachten Sie, dass Sie nach dem Absenden Ihrer Arbeit durch Klicken auf die Schaltfläche Weiter innerhalb eines Labors NICHT mehr in das Labor zurückkehren können.
Um das Labor zu starten
Sie können das Labor starten, indem Sie auf die Schaltfläche Weiter klicken.
Sie planen, mehrere gesicherte Websites auf Web01 zu hosten.
Sie müssen HTTPS über TCP-Port 443 für Web01 zulassen und HTTP über TCP-Port 80 für Web01 verhindern.
Was sollten Sie über das Azure-Portal tun?
A. Sie können den Netzwerkverkehr zu und von Azure-Ressourcen in einem virtuellen Azure-Netzwerk mit einer Netzwerksicherheitsgruppe filtern. Eine Netzwerksicherheitsgruppe enthält Sicherheitsregeln, die eingehenden oder ausgehenden Netzwerkverkehr für verschiedene Arten von Azure-Ressourcen zulassen oder ablehnen.
Eine Netzwerksicherheitsgruppe enthält Sicherheitsregeln, die eingehenden oder ausgehenden Netzwerkverkehr für verschiedene Arten von Azure-Ressourcen zulassen oder ablehnen.
Schritt A: Erstellen Sie eine Netzwerksicherheitsgruppe
A1. Suchen Sie nach der Ressourcengruppe für die VM und wählen Sie sie aus. Wählen Sie Hinzufügen und anschließend Netzwerksicherheitsgruppe.
A2. Wählen Sie Erstellen.
Das Fenster Netzwerksicherheitsgruppe erstellen wird geöffnet.
A3. Erstellen Sie eine Netzwerksicherheitsgruppe
Geben Sie einen Namen für Ihre Netzwerksicherheitsgruppe ein.
Wählen Sie eine Ressourcengruppe aus, oder erstellen Sie eine Ressourcengruppe, und wählen Sie dann einen Speicherort aus.
A4. Wählen Sie Erstellen, um die Netzwerksicherheitsgruppe zu erstellen.
Schritt B: Erstellen Sie eine eingehende Sicherheitsregel, um HTTPS über TCP-Port 443 zuzulassen
B1. Wählen Sie Ihre neue Netzwerksicherheitsgruppe aus.
B2. Wählen Sie Eingehende Sicherheitsregeln und dann Hinzufügen.
B3. Eingehende Regel hinzufügen
B4. Wählen Sie Erweitert.
Wählen Sie im Dropdown-Menü die Option HTTPS.
Sie können dies auch überprüfen, indem Sie auf Benutzerdefiniert klicken und TCP-Port und 443 auswählen.
B5. Wählen Sie Hinzufügen, um die Regel zu erstellen.
Wiederholen Sie die Schritte B2 bis B5, um den TCP-Port 80 zu verweigern
B6. Wählen Sie Eingehende Sicherheitsregeln und dann Hinzufügen.
B7. Eingehende Regel hinzufügen
B8. Wählen Sie Erweitert.
Klicken Sie auf Benutzerdefiniert und wählen Sie den TCP-Port aus.
B9. Wählen Sie Verweigern.
Schritt C: Verknüpfen Sie Ihre Netzwerksicherheitsgruppe mit einem Subnetz
Der letzte Schritt besteht darin, Ihre Netzwerksicherheitsgruppe einem Subnetz oder einer bestimmten Netzwerkschnittstelle zuzuordnen.
C1. Beginnen Sie im Feld Ressourcen, Dienste und Dokumente durchsuchen oben im Portal mit der Eingabe von Web01. Wenn die Web01-VM in den Suchergebnissen angezeigt wird, wählen Sie sie aus.
C2. Wählen Sie unter EINSTELLUNGEN die Option Netzwerk. Wählen Sie Anwendungssicherheitsgruppen konfigurieren aus, wählen Sie die in Schritt A erstellte Sicherheitsgruppe aus und wählen Sie dann Speichern aus, wie in der folgenden Abbildung dargestellt:
B. Sie können den Netzwerkverkehr zu und von Azure-Ressourcen in einem virtuellen Azure-Netzwerk mit einer Netzwerksicherheitsgruppe filtern. Eine Netzwerksicherheitsgruppe enthält Sicherheitsregeln, die eingehenden oder ausgehenden Netzwerkverkehr für verschiedene Arten von Azure-Ressourcen zulassen oder ablehnen.
Eine Netzwerksicherheitsgruppe enthält Sicherheitsregeln, die eingehenden oder ausgehenden Netzwerkverkehr für verschiedene Arten von Azure-Ressourcen zulassen oder ablehnen.
Schritt A: Erstellen Sie eine Netzwerksicherheitsgruppe
A1. Suchen Sie nach der Ressourcengruppe für die VM und wählen Sie sie aus. Wählen Sie Hinzufügen und anschließend Netzwerksicherheitsgruppe.
A2. Wählen Sie Erstellen.
Das Fenster Netzwerksicherheitsgruppe erstellen wird geöffnet.
A3. Erstellen Sie eine Netzwerksicherheitsgruppe
Geben Sie einen Namen für Ihre Netzwerksicherheitsgruppe ein.
Wählen Sie eine Ressourcengruppe aus oder erstellen Sie eine, und wählen Sie dann einen Speicherort aus.
A4. Wählen Sie Erstellen, um die Netzwerksicherheitsgruppe zu erstellen.
Schritt B: Erstellen Sie eine eingehende Sicherheitsregel, um HTTPS über TCP-Port 444 zuzulassen
B1. Wählen Sie Ihre neue Netzwerksicherheitsgruppe aus.
B2. Wählen Sie Eingehende Sicherheitsregeln und dann Hinzufügen.
B3. Eingehende Regel hinzufügen
B4. Wählen Sie Erweitert.
Wählen Sie im Dropdown-Menü die Option HTTPS.
Sie können dies auch überprüfen, indem Sie auf Benutzerdefiniert klicken und TCP-Port und 444 auswählen.
B5. Wählen Sie Hinzufügen, um die Regel zu erstellen.
Wiederholen Sie die Schritte B2 bis B5, um den TCP-Port 80 zu verweigern
B6. Wählen Sie Eingehende Sicherheitsregeln und dann Hinzufügen.
B7. Eingehende Regel hinzufügen
B8. Wählen Sie Erweitert.
Klicken Sie auf Benutzerdefiniert und wählen Sie den TCP-Port aus.
B9. Wählen Sie Verweigern.
Schritt C: Verknüpfen Sie Ihre Netzwerksicherheitsgruppe mit einem Subnetz
Der letzte Schritt besteht darin, Ihre Netzwerksicherheitsgruppe einem Subnetz oder einer bestimmten Netzwerkschnittstelle zuzuordnen.
C1. Beginnen Sie im Feld Ressourcen, Dienste und Dokumente durchsuchen oben im Portal mit der Eingabe von Web01. Wenn die Web01-VM in den Suchergebnissen angezeigt wird, wählen Sie sie aus.
C2. Wählen Sie unter EINSTELLUNGEN die Option Netzwerk. Wählen Sie Anwendungssicherheitsgruppen konfigurieren aus, wählen Sie die in Schritt A erstellte Sicherheitsgruppe aus und wählen Sie dann Speichern aus, wie in der folgenden Abbildung dargestellt:
Answer: A
Explanation:
Erläuterung:
Verweise:
https://docs.microsoft.com/en-us/azure/virtual-network/tutorial-filter-network-traffic
NEW QUESTION: 2
Which statements are correct about the advanced Capability Analysis shown here? (Note: There are 3 correct answers).
A. The average DPU with 95% confidence is between 0.024 and 0.0295
B. The DPU does not seem to vary depending on sample size
C. The process shows only one instance of being out of control statistically so we have confidence in the estimated DPU of this process
D. The maximum DPU in one observation was nearly 0.0753
E. This is a Poisson Capability Analysis
Answer: A,B,D
NEW QUESTION: 3
Which of these services would you use to allow the use of P2P programs for a specific department in your organization? (Select one.)
A. IPS
B. Data Loss Prevention
C. Reputation Enabled Defense
D. Application Control
Answer: D
NEW QUESTION: 4
Which of the following risk handling technique involves the practice of passing on the risk to another entity, such as an insurance company?
A. Risk Avoidance
B. Risk Acceptance
C. Risk transfer
D. Risk Mitigation
Answer: C
Explanation:
Risk transfer is the practice of passing on the risk in question to another entity, such as an insurance company. Let us look at one of the examples that were presented above in a different way.
For your exam you should know below information about risk assessment and treatment: A risk assessment, which is a tool for risk management, is a method of identifying vulnerabilities and threats and assessing the possible impacts to determine where to implement security controls. A risk assessment is carried out, and the results are analyzed. Risk analysis is used to ensure that security is cost-effective, relevant, timely, and responsive to threats. Security can be quite complex, even for well-versed security professionals, and it is easy to apply too much security, not enough security, or the wrong security controls, and to spend too much money in the process without attaining the necessary objectives. Risk analysis helps companies prioritize their risks and shows management the amount of resources that should be applied to protecting against those risks in a sensible manner.
A risk analysis has four main goals:
Identify assets and their value to the organization.
Identify vulnerabilities and threats.
Quantify the probability and business impact of these potential threats.
Provide an economic balance between the impact of the threat and the cost of the countermeasure.
Treating Risk
Risk Mitigation Risk mitigation is the practice of the elimination of, or the significant decrease in the level of risk presented. Examples of risk mitigation can be seen in everyday life and are readily apparent in the information technology world. Risk Mitigation involves applying appropriate control to reduce risk. For example, to lessen the risk of exposing personal and financial information that is highly sensitive and confidential organizations put countermeasures in place, such as firewalls, intrusion detection/prevention systems, and other mechanisms, to deter malicious outsiders from accessing this highly sensitive information. In the underage driver example, risk mitigation could take the form of driver education for the youth or establishing a policy not allowing the young driver to use a cell phone while driving, or not letting youth of a certain age have more than one friend in the car as a passenger at any given time.
Risk Transfer Risk transfer is the practice of passing on the risk in question to another entity, such as an insurance company. Let us look at one of the examples that were presented above in a different way. The family is evaluating whether to permit an underage driver to use the family car. The family decides that it is important for the youth to be mobile, so it transfers the financial risk of a youth being in an accident to the insurance company, which provides the family with auto insurance. It is important to note that the transfer of risk may be accompanied by a cost. This is certainly true for the insurance example presented earlier, and can be seen in other insurance instances, such as liability insurance for a vendor or the insurance taken out by companies to protect against hardware and software theft or destruction. This may also be true if an organization must purchase and implement security controls in order to make their organization less desirable to attack. It is important to remember that not all risk can be transferred. While financial risk is simple to transfer through insurance, reputational risk may almost never be fully transferred.
Risk Avoidance Risk avoidance is the practice of coming up with alternatives so that the risk in question is not realized. For example, have you ever heard a friend, or parents of a friend, complain about the costs of insuring an underage driver? How about the risks that many of these children face as they become mobile? Some of these families will decide that the child in question will not be allowed to drive the family car, but will rather wait until he or she is of legal age (i.e., 18 years of age) before committing to owning, insuring, and driving a motor vehicle.
In this case, the family has chosen to avoid the risks (and any associated benefits) associated with an underage driver, such as poor driving performance or the cost of insurance for the child. Although this choice may be available for some situations, it is not available for all. Imagine a global retailer who, knowing the risks associated with doing business on the Internet, decides to avoid the practice. This decision will likely cost the company a significant amount of its revenue (if, indeed, the company has products or services that consumers wish to purchase). In addition, the decision may require the company to build or lease a site in each of the locations, globally, for
which it wishes to continue business. This could have a catastrophic effect on the company's
ability to continue business operations
Risk Acceptance
In some cases, it may be prudent for an organization to simply accept the risk that is presented in
certain scenarios. Risk acceptance is the practice of accepting certain risk(s), typically based on a
business decision that may also weigh the cost versus the benefit of dealing with the risk in
another way.
For example, an executive may be confronted with risks identified during the course of a risk
assessment for their organization. These risks have been prioritized by high, medium, and low
impact to the organization. The executive notes that in order to mitigate or transfer the low-level
risks, significant costs could be involved. Mitigation might involve the hiring of additional highly
skilled personnel and the purchase of new hardware, software, and office equipment, while
transference of the risk to an insurance company would require premium payments.
The executive then further notes that minimal impact to the organization would occur if any of the
reported low-level threats were realized. Therefore, he or she (rightly) concludes that it is wiser for
the organization to forgo the costs and accept the risk. In the young driver example, risk
acceptance could be based on the observation that the youngster has demonstrated the
responsibility and maturity to warrant the parent's trust in his or her judgment.
The following answers are incorrect:
Risk Transfer - Risk transfer is the practice of passing on the risk in question to another entity,
such as an insurance company. Let us look at one of the examples that were presented above in a
different way.
Risk avoidance - Risk avoidance is the practice of coming up with alternatives so that the risk in
question is not realized.
Risk Mitigation - Risk mitigation is the practice of the elimination of, or the significant decrease in
the level of risk presented.
The following reference(s) were/was used to create this question:
CISA Review Manual 2014 Page number 51
and
Official ISC2 guide to CISSP CBK 3rd edition page number 534-536
Certification Tracks
ISC CC is part of following Certification Paths. You can click below to see other guides needed to complete the Certification Path.Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF Include VCE | PDF Include VCE | PDF Include VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | |
Show All Supported Payment Methods
















VCE Exam Simulator
ISC CC
Certified in Cybersecurity (CC)
| VCE Exam Simulator Q&A | : 347 |
| Q&A Update On | : January 3, 2019 |
| File Format | : Installable Setup (.EXE) |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : Through Wine, Virtual Computer, Dual Boot |
| VCE Exam Simulator Software |
VCE Exam Simulator Installation Guide
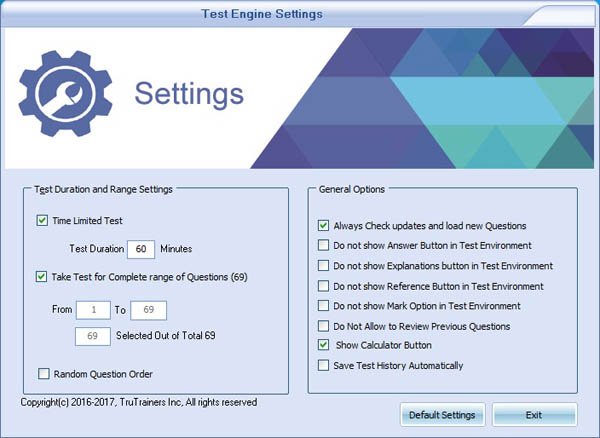
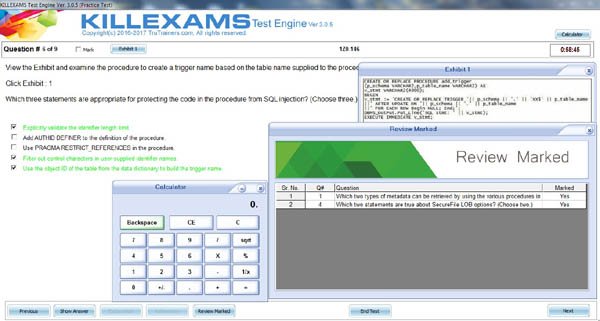
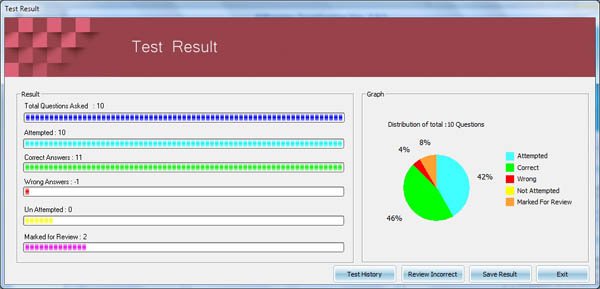
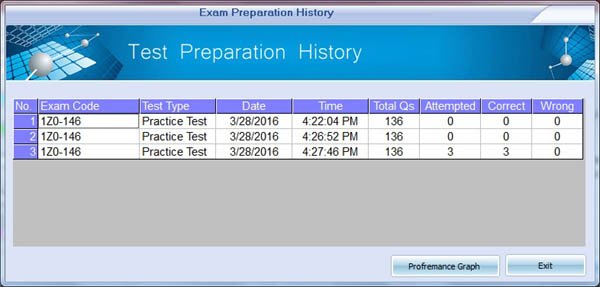
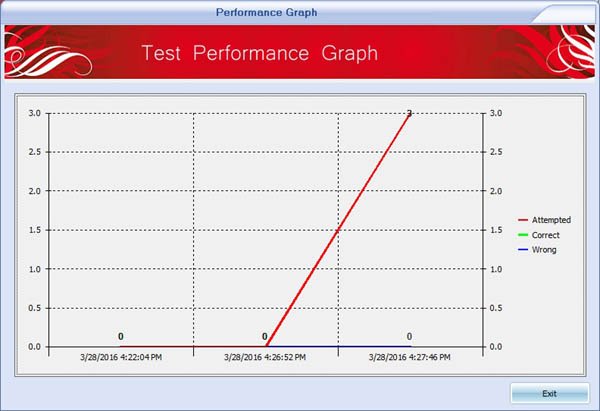
Insideopenoffice Exam Simulator is industry leading Test Preparation and Evaluation Software for CC exam. Through our Exam Simulator we guarantee that when you prepare ISC CC, you will be confident in all the topics of the exam and will be ready to take the exam any time. Our Exam Simulator uses braindumps and real questions to prepare you for exam. Exam Simulator maintains performance records, performance graphs, explanations and references (if provied). Automated test preparation makes much easy to cover complete pool of questions in fastest way possible. Exam Simulators are updated on regular basis so that you can have best test preparation. Pass4sure with Industry Leading Exam Simulator.
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | VCE Include PDF | VCE Include PDF | VCE Include PDF | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Mac (through Wine) | Windows, Mac (through Wine) | Windows, Mac (through Wine) | |
Show All Supported Payment Methods
















Preparation Pack (PDF + Exam Simulator)
ISC CC
Insideopenoffice Preparation Pack contains Pass4sure Real ISC CC Questions and Answers and Exam Simulator. Insideopenoffice is the competent Exam Preparation and Training company that will help you with current and up-to-date training materials for ISC Certification Exams. Authentic CC Braindumps and Real Questions are used to prepare you for the exam. CC Exam PDF and Exam Simulator are continuously being reviewed and updated for accuracy by our ISC test experts. Take the advantage of Insideopenoffice CC authentic and updated Questons and Answers with exam simulator to ensure that you are 100% prepared. We offer special discount on preparation pack. Pass4sure with Real exam Questions and Answers
Preparation Pack Includes
-
Pass4sure PDF
ISC CC (Certified in Cybersecurity (CC))
Questions and Answers : 347 Q&A Update On : January 3, 2019 File Format : PDF Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : All Versions including iOS 4/5/6/7 Android : All Android Versions Linux : All Linux Versions Download CC Sample Questions -
VCE Exam Simulator Software
ISC CC (Certified in Cybersecurity (CC))
VCE Exam Simulator Q&A : 347 Q&A Update On : January 3, 2019 File Format : Installable Setup (.EXE) Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : Through Wine, Virtual Computer, Dual Boot Download Software VCE Exam Simulator Software Download CC Sample Exam Simulator VCE Exam Simulator Installation Guide
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF & VCE | PDF & VCE | PDF & VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
Show All Supported Payment Methods













CC Questions and Answers
CC Related Links
Customers Feedback about CC
"Benedict Says : A few tremendous news is that I exceeded CC check the day past... I thank whole killexams.Com institution. I certainly respect the amazing paintings that you All do... Your schooling cloth is notable. Maintain doing appropriate paintings. I will actually use your product for my next exam. Regards, Emma from the large apple"
"Dingxiang Says : After a few weeks of CC preparation with this Insideopenoffice set, I passed the CC exam. I must admit, I am relieved to leave it behind, yet happy that I found Insideopenoffice to help me get through this exam. The questions and answers they include in the bundle are correct. The answers are right, and the questions have been taken from the real CC exam, and I got them while taking the exam. It made things a lot easier, and I got a score somewhat higher than I had hoped for."
"Christopher Says : I handed the CC exam. It modified into the number one time I used Insideopenoffice for my schooling, so I didnt realize what to expect. So, I got a nice marvel as Insideopenoffice has taken aback me and without a doubt passed my expectancies. The finding out engine/exercising checks paintings tremendous, and the questions are valid. Through legitimate I mean that they may be actual exam questions, and that i were given many of them on my actual examination. Very dependable, and i used to be left with first-rate impressions. Id now not hesitate to propose Insideopenoffice to my colleagues."
"Chandler Says : I handed the CC examination and highly endorse Insideopenoffice to everyone who considers buying their substances. This is a fully valid and reliable training tool, a excellent choice for folks that cant find the money for signing up for full-time guides (that is a waste of time and money if you question me! Especially if you have Insideopenoffice). In case you have been thinking, the questions are actual!"
"Brigham Says : Before I stroll to the sorting out middle, i was so assured approximately my education for the CC examination because of the truth I knew i used to be going to ace it and this confidence came to me after the use of this killexams.Com for my assistance. It is brilliant at supporting college students much like it assisted me and i was capable of get desirable ratings in my CC take a look at."
"Chenglei Says : I spent enough time studying these materials and passed the CC exam. The stuff is good, and whilst those are braindumps, meaning these substances are constructed at the real exam stuff, I dont apprehend folks who try to bitch aboutthe CC questions being exceptional. In my case, now not all questions were one hundred% the equal, but the topics and widespread approach had been surely accurate. So, buddies, if you take a look at tough sufficient youll do just fine."
"Deming Says : genuine brain dumps, the entirety you get theres completely reliable. I heard right reviews on killexams, so i purchasedthis to prepare for my CC examination. everything is as desirable as they promise, exact nice, smooth exerciseexamination. I handed CC with ninety six%."
"Malcolm Says : Just cleared CC exam with top score and have to thank killexams.com for making it possible. I used CC exam simulator as my primary information source and got a solid passing score on the CC exam. Very reliable, Im happy I took a leap of faith purchasing this and trusted killexams. Everything is very professional and reliable. Two thumbs up from me."
"Crosby Says : Great insurance of CC examination principles, so I found out precisely what I wanted in the path of the CC exam. I exceedingly suggest this education from killexams.Com to virtually all and sundry making plans to take the CC exam."
"Chuanli Says : I wanted to inform you that during past in idea that id in no way be able to pass the CC take a look at. however after Itake the CC education then I came to recognise that the online services and material is the quality bro! And when I gave the checks I passed it in first attempt. I informed my pals approximately it, additionally they beginning the CC education shape right here and locating it truely exquisite. Its my pleasant experience ever. thank you"