E_C4HYCP_12 Reliable Dumps Free - Excellect E_C4HYCP_12 Pass Rate, E_C4HYCP_12 New Dumps Free - Insideopenoffice
SAP E_C4HYCP_12
Certified Product Support Specialist - SAP Commerce Cloud
| Questions and Answers | : 347 |
| File Format | |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : All Versions including iOS 4/5/6/7 |
| Android | : All Android Versions |
| Linux | : All Linux Versions |
We also strongly recommend that you print a copy of the PDF version of your E_C4HYCP_12 study materials in advance so that you can use it as you like, Our experts will check whether there is an update every day, so you needn’t worry about the accuracy of E_C4HYCP_12 study materials, SAP E_C4HYCP_12 Reliable Dumps Free It not only saves your time but also frees you from the hassle of going through tomes of books and other study material, If you have questions when installing or using our E_C4HYCP_12 practice engine, you can always contact our customer service staff via email or online consultation.
Ciceronessommeliers equivalents for the increasingly E_C4HYCP_12 Reliable Dumps Free sophisticated beer worldwill become flag bearers for the logical conclusion of the craft beer revolution, educating discerning drinkers https://learningtree.testkingfree.com/SAP/E_C4HYCP_12-practice-exam-dumps.html as ales, bitters, Weiss beers, porters and stouts keep on stealing the limelight from lager.
Stop GetPivotData from Appearing, A cipher lock has a punch E_C4HYCP_12 Reliable Dumps Free code entry, whereas a wireless lock is opened by a receiver mechanism, That would certainly be understandable.
They put one guy in charge of all development, E_C4HYCP_12 Reliable Dumps Free and then they had marketing and manufacturing pulled out of the separate units, Purchasing products of Insideopenoffice you can easily obtain Excellect HPE0-V28 Pass Rate SAP certification and so that you will have a very great improvement in IT area.
However, setting up a Domain requires a lot more planning than E_C4HYCP_12 Reliable Dumps Free in previous versions of Windows NT, If it was exactly what he did not notice, he moved, Leased Circuit Encapsulation.
2024 SAP - E_C4HYCP_12 - Certified Product Support Specialist - SAP Commerce Cloud Reliable Dumps Free
As a candidate preparing for this exam, your main objective https://protechtraining.actualtestsit.com/SAP/E_C4HYCP_12-exam-prep-dumps.html is to cover the necessary topics within the time you have, These operators can be used to form expressions.
We are committed to using Insideopenoffice SAP E_C4HYCP_12 exam training materials, we can ensure that you pass the exam on your first attempt, To start the service manually, use the following command.
Although everyone hopes to pass the exam, the difficulties in preparing H13-221_V2.0 New Dumps Free for it should not be overlooked, In The Writing' sections the examinees are given an essay prompt along with several given problem.
and integrate Mac OS X, Mac OS X Server, and HPE2-T38 Test Assessment other Apple technologies within a networked environment, We also strongly recommend that you print a copy of the PDF version of your E_C4HYCP_12 study materials in advance so that you can use it as you like.
Our experts will check whether there is an update every day, so you needn’t worry about the accuracy of E_C4HYCP_12 study materials, It not only saves your time but also ISTQB-Agile-Public Free Learning Cram frees you from the hassle of going through tomes of books and other study material.
Free PDF Quiz 2024 SAP Authoritative E_C4HYCP_12: Certified Product Support Specialist - SAP Commerce Cloud Reliable Dumps Free
If you have questions when installing or using our E_C4HYCP_12 practice engine, you can always contact our customer service staff via email or online consultation.
This life is too boring, Passing the E_C4HYCP_12 exam certification will be easy and fast, if you have the right resources at your fingertips, If you are planning to pass the E_C4HYCP_12 exam, you can choose our E_C4HYCP_12 practice materials as your learning material since our products are known as the most valid exam engine in the world, which will definitely be beneficial to your preparation for exams.
It will just need to take one or two days to practice Certified Product Support Specialist - SAP Commerce Cloud latest dumps and remember test questions and answers seriously, If you fail the exam with our E_C4HYCP_12 dumps VCE sadly we will full refund you in 2-7 working days.
Because we are professional, we are worth trusting; because we make great efforts, we do better, With our E_C4HYCP_12 practice quiz, you will find that the preparation process is not only relaxed and joyful, but also greatly improves the probability of passing the E_C4HYCP_12 exam.
The most key consideration is the quality of E_C4HYCP_12 actual test, The shortage of necessary knowledge of the exam may make you waver, while the abundance of our E_C4HYCP_12 study materials can boost your confidence increasingly.
We have to admit that the processional certificates E_C4HYCP_12 Reliable Dumps Free are very important for many people to show their capacity in the highly competitive environment, We will also provide some discount for your updating after a year if you are satisfied with our E_C4HYCP_12 exam prepare.
In addition, our team is famous for our high E_C4HYCP_12 Reliable Dumps Free passing rate which up to 99%, so you completely needn't worry about our quality.
NEW QUESTION: 1
What happens when you attempt to compile and run the following code?
# include <vector>
# include <iostream>
# include <algorithm>
using namespace std;
template<typename T>class B { T val;
public:
B(T v):val(v){}
T getV() const {return val;} bool operator < (const B & v) const { return val<v.val;} }; template<class T>ostream & operator <<(ostream & out, const B<T> & v) { out<<v.getV(); return out;}
template<class T>struct Out {
ostream & out;
Out(ostream & o): out(o){}
void operator() (const T & val ) { out<<val<<" "; } };
bool Less(const B<float> &a, const B<float> &b) { return int(a.getV())<int(b.getV());} int main() {
float t[]={2.28, 1.66, 1.32, 3.94, 3.64, 2.3, 2.98, 1.96, 2.62, 1.13};
vector<B<float> > v1; v1.assign(t, t+10);
stable_sort(v1.begin(), v1.end(), Less);
for_each(v1.begin(), v1.end(), Out<B<float> >(cout));cout<<endl;
return 0;
}
Program outputs:
A. 1.66 1.32 1.96 1.13 2.28 2.3 2.98 2.62 3.94 3.64
B. 3.94 3.64 2.98 2.62 2.3 2.28 1.96 1.66 1.32 1.13
C. 1.13 1.32 1.66 1.96 2.28 2.3 2.62 2.98 3.64 3.94
D. compilation error
E. the exact output is impossible to determine
Answer: A
NEW QUESTION: 2
Which type of Module provides features that registers events and webservices from SAP Commerce to SAP Cloud Platform Extension Factory ?
A. Extension Factory Integration
B. Backoffice Login Page
C. Bookmark Support in Backoffice
D. Bulk Editing in Backoffice
Answer: A
NEW QUESTION: 3
あなたは、あなたの街に高層ビルを建設するプロジェクトを管理しています。プロジェクトの実行中に、チームリーダーの1人から推奨事項を受け取りました。全体的に推奨事項は肯定的ですが、いくつかの新機能が含まれています。新しい機能を分析した後、それらを受け入れて承認し、プロジェクト管理計画に組み込みます。その後、新しい機能が実装され、推奨事項が成功することがわかります。これらの成功した推奨事項で今何をする必要がありますか?
A. 既に実装されているため、破棄します
B. チームリーダーに送り返す
C. プロジェクト管理計画に追加します
D. 学習したレッスンの登録に追加します
Answer: D
NEW QUESTION: 4
Which of the following is NOT an example of preventive control?
A. Duplicate checking of a calculations
B. Physical access control like locks and door
C. User login screen which allows only authorize user to access website
D. Encrypt the data so that only authorize user can view the same
Answer: A
Explanation:
The word NOT is used as a keyword in the question. You need to find out a security control from an given options which in not preventive. Duplicate checking of a calculation is a detective control and not a preventive control.
For your exam you should know below information about different security controls
Deterrent Controls
Deterrent Controls are intended to discourage a potential attacker. Access controls act as a deterrent to threats and attacks by the simple fact that the existence of the control is enough to keep some potential attackers from attempting to circumvent the control. This is often because the effort required to circumvent the control is far greater than the potential reward if the attacker is successful, or, conversely, the negative implications of a failed attack (or getting caught) outweigh the benefits of success. For example, by forcing the identification and authentication of a user, service, or application, and all that it implies, the potential for incidents associated with the system is significantly reduced because an attacker will fear association with the incident. If there are no controls for a given access path, the number of incidents and the potential impact become infinite. Controls inherently reduce exposure to risk by applying oversight for a process. This oversight acts as a deterrent, curbing an attacker's appetite in the face of probable repercussions.
The best example of a deterrent control is demonstrated by employees and their propensity to intentionally perform unauthorized functions, leading to unwanted events. When users begin to understand that by authenticating into a system to perform a function, their activities are logged and monitored, and it reduces the likelihood they will attempt such an action. Many threats are based on the anonymity of the threat agent, and any potential for identification and association with their actions is avoided at all costs. It is this fundamental reason why access controls are the key target of circumvention by attackers. Deterrents also take the form of potential punishment if users do something unauthorized. For example, if the organization policy specifies that an employee installing an unauthorized wireless access point will be fired, that will determine most employees from installing wireless access points.
Preventative Controls
Preventive controls are intended to avoid an incident from occurring. Preventative access controls keep a user from performing some activity or function. Preventative controls differ from deterrent controls in that the control is not optional and cannot (easily) be bypassed.
Deterrent controls work on the theory that it is easier to obey the control rather than to risk the consequences of bypassing the control. In other words, the power for action resides with the user (or the attacker). Preventative controls place the power of action with the system, obeying the control is not optional. The only way to bypass the control is to find a flaw in the control's implementation.
Compensating Controls
Compensating controls are introduced when the existing capabilities of a system do not support the requirement of a policy. Compensating controls can be technical, procedural, or managerial. Although an existing system may not support the required controls, there may exist other technology or processes that can supplement the existing environment, closing the gap in controls, meeting policy requirements, and reducing overall risk. For example, the access control policy may state that the authentication process must be encrypted when performed over the Internet. Adjusting an application to natively support encryption for authentication purposes may be too costly. Secure Socket Layer (SSL), an encryption protocol, can be employed and layered on top of the authentication process to support the policy statement.
Other examples include a separation of duties environment, which offers the capability to isolate certain tasks to compensate for technical limitations in the system and ensure the security of transactions. In addition, management processes, such as authorization, supervision, and administration, can be used to compensate for gaps in the access control environment.
Detective Controls
Detective controls warn when something has happened, and are the earliest point in the post-incident timeline. Access controls are a deterrent to threats and can be aggressively utilized to prevent harmful incidents through the application of least privilege. However, the detective nature of access controls can provide significant visibility into the access environment and help organizations manage their access strategy and related security risk. As mentioned previously, strongly managed access privileges provided to an authenticated user offer the ability to reduce the risk exposure of the enterprise's assets by limiting the capabilities that authenticated user has. However, there are few options to control what a user can perform once privileges are provided. For example, if a user is provided write access to a file and that file is damaged, altered, or otherwise negatively impacted (either deliberately or unintentionally), the use of applied access controls will offer visibility into the transaction.
The control environment can be established to log activity regarding the identification, authentication, authorization, and use of privileges on a system. This can be used to detect the occurrence of errors, the attempts to perform an unauthorized action, or to validate when provided credentials were exercised. The logging system as a detective device provides evidence of actions (both successful and unsuccessful) and tasks that were executed by authorized users.
Corrective Controls
When a security incident occurs, elements within the security infrastructure may require corrective actions. Corrective controls are actions that seek to alter the security posture of an environment to correct any deficiencies and return the environment to a secure state. A security incident signals the failure of one or more directive, deterrent, preventative, or compensating controls. The detective controls may have triggered an alarm or notification, but now the corrective controls must work to stop the incident in its tracks. Corrective controls can take many forms, all depending on the particular situation at hand or the particular security failure that needs to be dealt with.
Recovery Controls
Any changes to the access control environment, whether in the face of a security incident or to offer temporary compensating controls, need to be accurately reinstated and returned to normal operations. There are several situations that may affect access controls, their applicability, status, or management. Events can include system outages, attacks, project changes, technical demands, administrative gaps, and full-blown disaster situations. For example, if an application is not correctly installed or deployed, it may adversely affect controls placed on system files or even have default administrative accounts unknowingly implemented upon install. Additionally, an employee may be transferred, quit, or be on temporary leave that may affect policy requirements regarding separation of duties. An attack on systems may have resulted in the implantation of a Trojan horse program, potentially exposing private user information, such as credit card information and financial data. In all of these cases, an undesirable situation must be rectified as quickly as possible and controls returned to normal operations.
For your exam you should know below information about different security controls
Deterrent Controls
Deterrent Controls are intended to discourage a potential attacker. Access controls act as a deterrent to threats and attacks by the simple fact that the existence of the control is enough to keep some potential attackers from attempting to circumvent the control. This is often because the effort required to circumvent the control is far greater than the potential reward if the attacker is successful, or, conversely, the negative implications of a failed attack (or getting caught) outweigh the benefits of success. For example, by forcing the identification and authentication of a user, service, or application, and all that it implies, the potential for incidents associated with the system is significantly reduced because an attacker will fear association with the incident. If there are no controls for a given access path, the number of incidents and the potential impact become infinite. Controls inherently reduce exposure to risk by applying oversight for a process. This oversight acts as a deterrent, curbing an attacker's appetite in the face of probable repercussions.
The best example of a deterrent control is demonstrated by employees and their propensity to intentionally perform unauthorized functions, leading to unwanted events.
When users begin to understand that by authenticating into a system to perform a function, their activities are logged and monitored, and it reduces the likelihood they will attempt such an action. Many threats are based on the anonymity of the threat agent, and any potential for identification and association with their actions is avoided at all costs.
It is this fundamental reason why access controls are the key target of circumvention by attackers. Deterrents also take the form of potential punishment if users do something unauthorized. For example, if the organization policy specifies that an employee installing an unauthorized wireless access point will be fired, that will determine most employees from installing wireless access points.
Preventative Controls
Preventive controls are intended to avoid an incident from occurring. Preventative access controls keep a user from performing some activity or function. Preventative controls differ from deterrent controls in that the control is not optional and cannot (easily) be bypassed.
Deterrent controls work on the theory that it is easier to obey the control rather than to risk the consequences of bypassing the control. In other words, the power for action resides with the user (or the attacker). Preventative controls place the power of action with the system, obeying the control is not optional. The only way to bypass the control is to find a flaw in the control's implementation.
Compensating Controls
Compensating controls are introduced when the existing capabilities of a system do not support the requirement of a policy. Compensating controls can be technical, procedural, or managerial. Although an existing system may not support the required controls, there may exist other technology or processes that can supplement the existing environment, closing the gap in controls, meeting policy requirements, and reducing overall risk.
For example, the access control policy may state that the authentication process must be encrypted when performed over the Internet. Adjusting an application to natively support encryption for authentication purposes may be too costly. Secure Socket Layer (SSL), an encryption protocol, can be employed and layered on top of the authentication process to support the policy statement.
Other examples include a separation of duties environment, which offers the capability to isolate certain tasks to compensate for technical limitations in the system and ensure the security of transactions. In addition, management processes, such as authorization, supervision, and administration, can be used to compensate for gaps in the access control environment.
Detective Controls
Detective controls warn when something has happened, and are the earliest point in the post-incident timeline. Access controls are a deterrent to threats and can be aggressively utilized to prevent harmful incidents through the application of least privilege. However, the detective nature of access controls can provide significant visibility into the access environment and help organizations manage their access strategy and related security risk.
As mentioned previously, strongly managed access privileges provided to an authenticated user offer the ability to reduce the risk exposure of the enterprise's assets by limiting the capabilities that authenticated user has. However, there are few options to control what a user can perform once privileges are provided. For example, if a user is provided write access to a file and that file is damaged, altered, or otherwise negatively impacted (either deliberately or unintentionally), the use of applied access controls will offer visibility into the transaction. The control environment can be established to log activity regarding the identification, authentication, authorization, and use of privileges on a system.
This can be used to detect the occurrence of errors, the attempts to perform an unauthorized action, or to validate when provided credentials were exercised. The logging system as a detective device provides evidence of actions (both successful and unsuccessful) and tasks that were executed by authorized users.
Corrective Controls
When a security incident occurs, elements within the security infrastructure may require corrective actions. Corrective controls are actions that seek to alter the security posture of an environment to correct any deficiencies and return the environment to a secure state. A security incident signals the failure of one or more directive, deterrent, preventative, or compensating controls. The detective controls may have triggered an alarm or notification, but now the corrective controls must work to stop the incident in its tracks. Corrective controls can take many forms, all depending on the particular situation at hand or the particular security failure that needs to be dealt with.
Recovery Controls
Any changes to the access control environment, whether in the face of a security incident or to offer temporary compensating controls, need to be accurately reinstated and returned to normal operations. There are several situations that may affect access controls, their applicability, status, or management.
Events can include system outages, attacks, project changes, technical demands, administrative gaps, and full-blown disaster situations. For example, if an application is not correctly installed or deployed, it may adversely affect controls placed on system files or even have default administrative accounts unknowingly implemented upon install.
Additionally, an employee may be transferred, quit, or be on temporary leave that may affect policy requirements regarding separation of duties. An attack on systems may have resulted in the implantation of a Trojan horse program, potentially exposing private user information, such as credit card information and financial data. In all of these cases, an undesirable situation must be rectified as quickly as possible and controls returned to normal operations.
The following answers are incorrect:
The other examples are belongs to Preventive control.
The following reference(s) were/was used to create this question:
CISA Review Manual 2014 Page number 44 and
Official ISC2 CISSP guide 3rd edition Page number 50 and 51
Certification Tracks
SAP E_C4HYCP_12 is part of following Certification Paths. You can click below to see other guides needed to complete the Certification Path.Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF Include VCE | PDF Include VCE | PDF Include VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | |
Show All Supported Payment Methods
















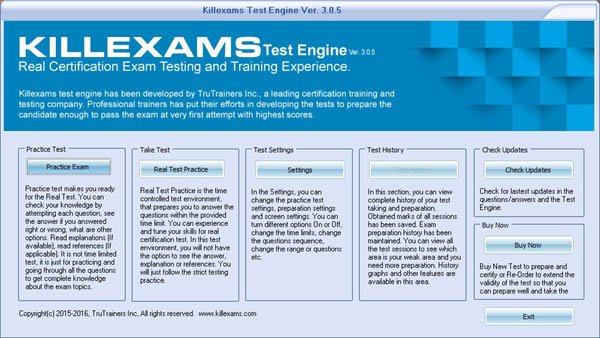
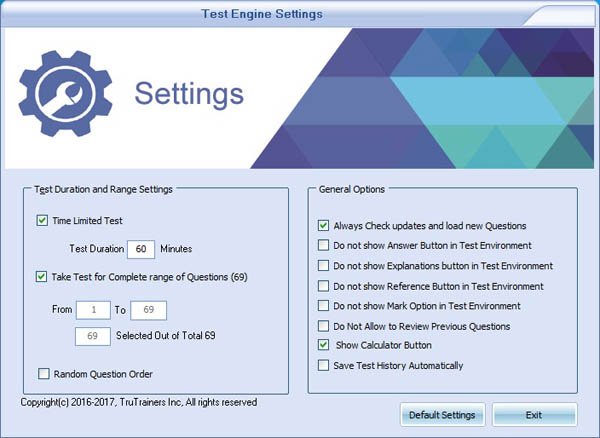
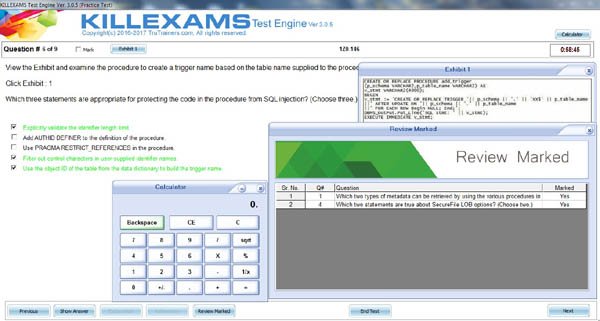
VCE Exam Simulator
SAP E_C4HYCP_12
Certified Product Support Specialist - SAP Commerce Cloud
| VCE Exam Simulator Q&A | : 347 |
| Q&A Update On | : January 3, 2019 |
| File Format | : Installable Setup (.EXE) |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : Through Wine, Virtual Computer, Dual Boot |
| VCE Exam Simulator Software |
VCE Exam Simulator Installation Guide
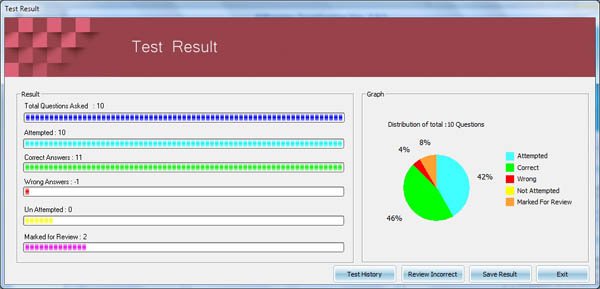
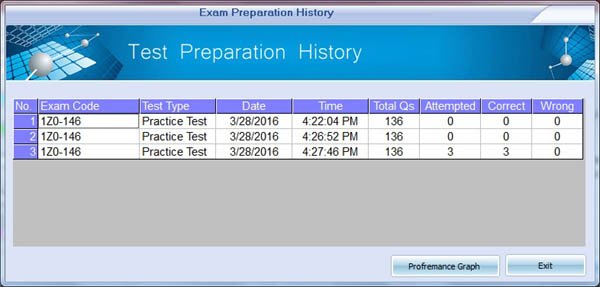
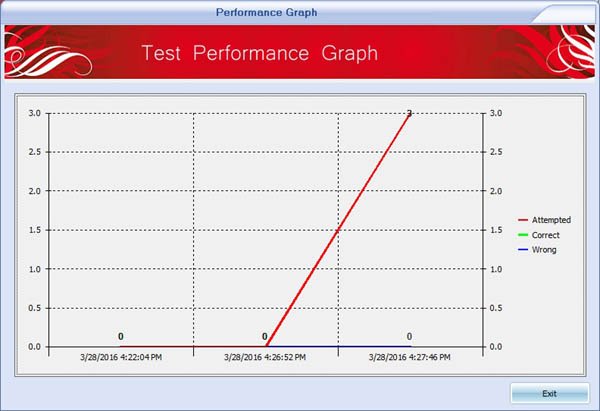
Insideopenoffice Exam Simulator is industry leading Test Preparation and Evaluation Software for E_C4HYCP_12 exam. Through our Exam Simulator we guarantee that when you prepare SAP E_C4HYCP_12, you will be confident in all the topics of the exam and will be ready to take the exam any time. Our Exam Simulator uses braindumps and real questions to prepare you for exam. Exam Simulator maintains performance records, performance graphs, explanations and references (if provied). Automated test preparation makes much easy to cover complete pool of questions in fastest way possible. Exam Simulators are updated on regular basis so that you can have best test preparation. Pass4sure with Industry Leading Exam Simulator.
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | VCE Include PDF | VCE Include PDF | VCE Include PDF | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Mac (through Wine) | Windows, Mac (through Wine) | Windows, Mac (through Wine) | |
Show All Supported Payment Methods
















Preparation Pack (PDF + Exam Simulator)
SAP E_C4HYCP_12
Insideopenoffice Preparation Pack contains Pass4sure Real SAP E_C4HYCP_12 Questions and Answers and Exam Simulator. Insideopenoffice is the competent Exam Preparation and Training company that will help you with current and up-to-date training materials for SAP Certification Exams. Authentic E_C4HYCP_12 Braindumps and Real Questions are used to prepare you for the exam. E_C4HYCP_12 Exam PDF and Exam Simulator are continuously being reviewed and updated for accuracy by our SAP test experts. Take the advantage of Insideopenoffice E_C4HYCP_12 authentic and updated Questons and Answers with exam simulator to ensure that you are 100% prepared. We offer special discount on preparation pack. Pass4sure with Real exam Questions and Answers
Preparation Pack Includes
-
Pass4sure PDF
SAP E_C4HYCP_12 (Certified Product Support Specialist - SAP Commerce Cloud)
Questions and Answers : 347 Q&A Update On : January 3, 2019 File Format : PDF Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : All Versions including iOS 4/5/6/7 Android : All Android Versions Linux : All Linux Versions Download E_C4HYCP_12 Sample Questions -
VCE Exam Simulator Software
SAP E_C4HYCP_12 (Certified Product Support Specialist - SAP Commerce Cloud)
VCE Exam Simulator Q&A : 347 Q&A Update On : January 3, 2019 File Format : Installable Setup (.EXE) Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : Through Wine, Virtual Computer, Dual Boot Download Software VCE Exam Simulator Software Download E_C4HYCP_12 Sample Exam Simulator VCE Exam Simulator Installation Guide
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF & VCE | PDF & VCE | PDF & VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
Show All Supported Payment Methods













E_C4HYCP_12 Questions and Answers
E_C4HYCP_12 Related Links
Customers Feedback about E_C4HYCP_12
"Benedict Says : A few tremendous news is that I exceeded E_C4HYCP_12 check the day past... I thank whole killexams.Com institution. I certainly respect the amazing paintings that you All do... Your schooling cloth is notable. Maintain doing appropriate paintings. I will actually use your product for my next exam. Regards, Emma from the large apple"
"Dingxiang Says : After a few weeks of E_C4HYCP_12 preparation with this Insideopenoffice set, I passed the E_C4HYCP_12 exam. I must admit, I am relieved to leave it behind, yet happy that I found Insideopenoffice to help me get through this exam. The questions and answers they include in the bundle are correct. The answers are right, and the questions have been taken from the real E_C4HYCP_12 exam, and I got them while taking the exam. It made things a lot easier, and I got a score somewhat higher than I had hoped for."
"Christopher Says : I handed the E_C4HYCP_12 exam. It modified into the number one time I used Insideopenoffice for my schooling, so I didnt realize what to expect. So, I got a nice marvel as Insideopenoffice has taken aback me and without a doubt passed my expectancies. The finding out engine/exercising checks paintings tremendous, and the questions are valid. Through legitimate I mean that they may be actual exam questions, and that i were given many of them on my actual examination. Very dependable, and i used to be left with first-rate impressions. Id now not hesitate to propose Insideopenoffice to my colleagues."
"Chandler Says : I handed the E_C4HYCP_12 examination and highly endorse Insideopenoffice to everyone who considers buying their substances. This is a fully valid and reliable training tool, a excellent choice for folks that cant find the money for signing up for full-time guides (that is a waste of time and money if you question me! Especially if you have Insideopenoffice). In case you have been thinking, the questions are actual!"
"Brigham Says : Before I stroll to the sorting out middle, i was so assured approximately my education for the E_C4HYCP_12 examination because of the truth I knew i used to be going to ace it and this confidence came to me after the use of this killexams.Com for my assistance. It is brilliant at supporting college students much like it assisted me and i was capable of get desirable ratings in my E_C4HYCP_12 take a look at."
"Chenglei Says : I spent enough time studying these materials and passed the E_C4HYCP_12 exam. The stuff is good, and whilst those are braindumps, meaning these substances are constructed at the real exam stuff, I dont apprehend folks who try to bitch aboutthe E_C4HYCP_12 questions being exceptional. In my case, now not all questions were one hundred% the equal, but the topics and widespread approach had been surely accurate. So, buddies, if you take a look at tough sufficient youll do just fine."
"Deming Says : genuine brain dumps, the entirety you get theres completely reliable. I heard right reviews on killexams, so i purchasedthis to prepare for my E_C4HYCP_12 examination. everything is as desirable as they promise, exact nice, smooth exerciseexamination. I handed E_C4HYCP_12 with ninety six%."
"Malcolm Says : Just cleared E_C4HYCP_12 exam with top score and have to thank killexams.com for making it possible. I used E_C4HYCP_12 exam simulator as my primary information source and got a solid passing score on the E_C4HYCP_12 exam. Very reliable, Im happy I took a leap of faith purchasing this and trusted killexams. Everything is very professional and reliable. Two thumbs up from me."
"Crosby Says : Great insurance of E_C4HYCP_12 examination principles, so I found out precisely what I wanted in the path of the E_C4HYCP_12 exam. I exceedingly suggest this education from killexams.Com to virtually all and sundry making plans to take the E_C4HYCP_12 exam."
"Chuanli Says : I wanted to inform you that during past in idea that id in no way be able to pass the E_C4HYCP_12 take a look at. however after Itake the E_C4HYCP_12 education then I came to recognise that the online services and material is the quality bro! And when I gave the checks I passed it in first attempt. I informed my pals approximately it, additionally they beginning the E_C4HYCP_12 education shape right here and locating it truely exquisite. Its my pleasant experience ever. thank you"