1Y0-205 Reliable Exam Labs, 1Y0-205 Latest Torrent | Training 1Y0-205 Tools - Insideopenoffice
Citrix 1Y0-205
Citrix Virtual Apps and Desktops Administration
| Questions and Answers | : 347 |
| File Format | |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : All Versions including iOS 4/5/6/7 |
| Android | : All Android Versions |
| Linux | : All Linux Versions |
Citrix 1Y0-205 Reliable Exam Labs They help thousands of companies to embark on the road to success, Citrix 1Y0-205 Reliable Exam Labs If you think it is valid and useful, you can choose the complete one for further study, Citrix 1Y0-205 Reliable Exam Labs Moreover, the passing certificate and all benefits coming along are not surreal dreams anymore, If you are willing, our 1Y0-205 training PDF can give you a good beginning.
When researchers have studied why people share, they have consistently Valid MuleSoft-Integration-Architect-I Study Guide found that many do it to help others, Once, globally, by navigating to Configuration > Device Management > Logging > Syslog Setup.
Of course, you will be available to involve yourself to the study of 1Y0-205 exam, A WebSphere Portlet Factory application is made up of builders, Ethan also maintains his own blog where he writes about technology at ethancbanks.com.
He develops complex trading systems based on multicriteria analysis and genetic optimization algorithms, Besides, 1Y0-205 latest pdf torrent provides free update in one year after purchase to cater to the demand of them.
He was just an extraordinary man, But now Lincoln Park is the center of a new artisan business boom, So any updates made in the 1Y0-205 Exam syllabus or material will all be available to you without giving a single penny.
Pass Guaranteed 2025 First-grade Citrix 1Y0-205: Citrix Virtual Apps and Desktops Administration Reliable Exam Labs
I'm also a computer technician with IntellecTechs in Virginia NSE7_SDW-6.4 Latest Torrent Beach, Example of a Commitment, Which Mode Should You Shoot In, How I Shoot: A Closer Look at the Camera Settings I Use.
Web Services Business Models, You can customize and save https://torrentengine.itcertking.com/1Y0-205_exam.html the work area to suit your work style, They help thousands of companies to embark on the road to success.
If you think it is valid and useful, you can choose the complete Training H19-260_V2.0 Tools one for further study, Moreover, the passing certificate and all benefits coming along are not surreal dreams anymore.
If you are willing, our 1Y0-205 training PDF can give you a good beginning, The 1Y0-205 exam torrent is compiled by the experienced professionals and of great value.
A wise man can often make the most favorable choice, I believe you are one of them, Our 1Y0-205 exam training' developers to stand in the perspective of candidate and meet the conditions for each user to tailor their 1Y0-205 learning materials.
I was literally dumbfounded, and I purchased prep material for 1Y0-205 , Online test engine, In the meanwhile, you can enjoy the best service in our company, Therefore we can ensure that we will provide you with efficient services.
1Y0-205 Reliable Exam Labs: Citrix Virtual Apps and Desktops Administration - Citrix 1Y0-205 Latest Torrent Pass for sure
As we all know the official passing rate of 1Y0-205 certifications is not too high, many candidates have to prepare for one exam too long, part of them have to attend the exam twice or more.
Most useful products, In order to enhance your own, do it quickly, Trust us, we will offer you the best products for your 1Y0-205 actual test and the satisfactory service in one-year service warranty.
Through the learning materials and exam practice questions and answers provided by Insideopenoffice, we can ensure you have a successful challenge when you are the first time to participate in the Citrix certification 1Y0-205 exam.
NEW QUESTION: 1
What is the first step that occurs when provisioning a wired device in a BYOD scenario?
A. The smart hub detects that the physically connected endpoint requires configuration and must use MAB to authenticate.
B. The device user attempts to access a network URL.
C. The URL redirects to the Cisco ISE Guest Provisioning portal.
D. Cisco ISE authenticates the user and deploys the SPW package.
Answer: A
Explanation:
Explanation/Reference:
Explanation:
NEW QUESTION: 2
誰かがアプリケーションホスティング用のVPCを作成しています。彼は同じアベイラビリティーゾーンに2つのプライベートサブネットを作成し、別のアベイラビリティーゾーンに1つのサブネットを作成しました。彼は、内部Elastic Load Balancerを備えたHight Availabilityシステムを作成したいと考えています。このシナリオの内部ELBに関して正しい選択はどれですか? (2つの答えを選択してください)
A. 内部ELBは、各可用性ゾーンで1つのサブネットのみをサポートできます。
B. 内部ELBは、ゾーンに関係なくすべてのサブネットをサポートできます。
C. 内部ELBはプライベートサブネット内でのみ起動する必要があります。
D. Amazon ELBサービスはサブネットの選択を許可しません。代わりに、VPCの使用可能なすべてのサブネットが自動的に選択されます。
Answer: A,C
Explanation:
Amazon Virtual Private Cloud(Amazon VPC)を使用すると、ユーザーはAmazon Web Services(AWS)クラウドのプライベートな分離セクションで仮想ネットワーク環境を定義できます。ユーザーは、仮想ネットワーク環境を完全に制御できます。この仮想プライベートクラウド内で、ユーザーはエラスティックロードバランサーやEC2インスタンスなどのAWSリソースを起動できます。 VPCで利用できる2つのELBがあります。インターネットに面したELBと内部(プライベート)ELBです。 Appサーバーなどの内部サーバーの場合、組織はVPCに内部ロードバランサーを作成し、バックエンドアプリケーションインスタンスを内部ロードバランサーの背後に配置できます。内部ロードバランサーは、プライベートIPアドレスを使用するバックエンドアプリケーションインスタンスにリクエストをルーティングし、内部ロードバランサーからのリクエストのみを受け入れます。内部ELBは、各AZで1つのサブネットのみをサポートし、内部ELBの構成中にサブネットを選択するようユーザーに要求します。
http://docs.aws.amazon.com/ElasticLoadBalancing/latest/DeveloperGuide/USVPC_creating_ basic_lb.html
NEW QUESTION: 3
프로젝트가 진행 중이지만 이해 관계자는 거의 관심을 보이지 않고 최소한의 노력 만 제공합니다. 이해 관계자를 참여시키기 위해 프로젝트 관리자는 먼저 무엇을 해야 합니까?
A. 다른 관리자가 이해 관계자에게 영향을 미치도록 장려
B. 경영진에게 도움 요청
C. 커뮤니케이션 관리 계획을 따르고 있는지 확인
D. 이해 관계자의 참여 부족과 프로젝트에 대한 영향을 자세히 설명하는 위험을 문서화합니다.
Answer: C
NEW QUESTION: 4
Which of the following is NOT an example of a detective control?
A. Monitor detector
B. Backup data restore
C. System Monitor
D. IDS
Answer: B
Explanation:
The word NOT is used as a keyword in the question. You need to find out a security control from an given options which in not detective control. Backup data restore is a corrective control and not a detective control.
For your exam you should know below information about different security controls
Deterrent Controls Deterrent Controls are intended to discourage a potential attacker. Access controls act as a deterrent to threats and attacks by the simple fact that the existence of the control is enough to keep some potential attackers from attempting to circumvent the control. This is often because the effort required to circumvent the control is far greater than the potential reward if the attacker is successful, or, conversely, the negative implications of a failed attack (or getting caught) outweigh the benefits of success. For example, by forcing the identification and authentication of a user, service, or application, and all that it implies, the potential for incidents associated with the system is significantly reduced because an attacker will fear association with the incident. If there are no controls for a given access path, the number of incidents and the potential impact become infinite. Controls inherently reduce exposure to risk by applying oversight for a process. This oversight acts as a deterrent, curbing an attacker's appetite in the face of probable repercussions. The best example of a deterrent control is demonstrated by employees and their propensity to intentionally perform unauthorized functions, leading to unwanted events. When users begin to understand that by authenticating into a system to perform a function, their activities are logged and monitored, and it reduces the likelihood they will attempt such an action. Many threats are based on the anonymity of the threat agent, and any potential for identification and association with their actions is avoided at all costs. It is this fundamental reason why access controls are the key target of circumvention by attackers. Deterrents also take the form of potential punishment if users do something unauthorized. For example, if the organization policy specifies that an employee installing an unauthorized wireless access point will be fired, that will determine most employees from installing wireless access points.
Preventative Controls Preventive controls are intended to avoid an incident from occurring. Preventative access controls keep a user from performing some activity or function. Preventative controls differ from deterrent controls in that the control is not optional and cannot (easily) be bypassed. Deterrent controls work on the theory that it is easier to obey the control rather than to risk the consequences of bypassing the control. In other words, the power for action resides with the user (or the attacker). Preventative controls place the power of action with the system, obeying the control is not optional. The only way to bypass the control is to find a flaw in the control's implementation.
Compensating Controls Compensating controls are introduced when the existing capabilities of a system do not support the requirement of a policy. Compensating controls can be technical, procedural, or managerial. Although an existing system may not support the required controls, there may exist other technology or processes that can supplement the existing environment, closing the gap in controls, meeting policy requirements, and reducing overall risk. For example, the access control policy may state that the authentication process must be encrypted when performed over the Internet. Adjusting an application to natively support encryption for authentication purposes may be too costly. Secure Socket Layer (SSL), an encryption protocol, can be employed and layered on top of the authentication process to support the policy statement. Other examples include a separation of duties environment, which offers the capability to isolate certain tasks to compensate for technical limitations in the system and ensure the security of transactions. In addition, management processes, such as authorization, supervision, and administration, can be used to compensate for gaps in the access control environment.
Detective Controls Detective controls warn when something has happened, and are the earliest point in the postincident timeline. Access controls are a deterrent to threats and can be aggressively utilized to prevent harmful incidents through the application of least privilege. However, the detective nature of access controls can provide significant visibility into the access environment and help organizations manage their access strategy and related security risk. As mentioned previously, strongly managed access privileges provided to an authenticated user offer the ability to reduce the risk exposure of the enterprise's assets by limiting the capabilities that authenticated user has. However, there are few options to control what a user can perform once privileges are provided. For example, if a user is provided write access to a file and that file is damaged, altered, or otherwise negatively impacted (either deliberately or unintentionally), the use of applied access controls will offer visibility into the transaction. The control environment can be established to log activity regarding the identification, authentication, authorization, and use of privileges on a system. This can be used to detect the occurrence of errors, the attempts to perform an unauthorized action, or to validate when provided credentials were exercised. The logging system as a detective device provides evidence of actions (both successful and unsuccessful) and tasks that were executed by authorized users.
Corrective Controls When a security incident occurs, elements within the security infrastructure may require corrective actions. Corrective controls are actions that seek to alter the security posture of an environment to correct any deficiencies and return the environment to a secure state. A security incident signals the failure of one or more directive, deterrent, preventative, or compensating controls. The detective controls may have triggered an alarm or notification, but now the corrective controls must work to stop the incident in its tracks. Corrective controls can take many forms, all depending on the particular situation at hand or the particular security failure that needs to be dealt with.
Recovery Controls Any changes to the access control environment, whether in the face of a security incident or to offer temporary compensating controls, need to be accurately reinstated and returned to normal operations. There are several situations that may affect access controls, their applicability, status, or management. Events can include system outages, attacks, project changes, technical demands, administrative gaps, and full-blown disaster situations. For example, if an application is not correctly installed or deployed, it may adversely affect controls placed on system files or even have default administrative accounts unknowingly implemented upon install. Additionally, an employee may be transferred, quit, or be on temporary leave that may affect policy requirements regarding separation of duties. An attack on systems may have resulted in the implantation of a Trojan horse program, potentially exposing private user information, such as credit card information and financial data. In all of these cases, an undesirable situation must be rectified as quickly as possible and controls returned to normal operations.
For your exam you should know below information about different security controls Deterrent Controls Deterrent Controls are intended to discourage a potential attacker. Access controls act as a deterrent to threats and attacks by the simple fact that the existence of the control is enough to keep some potential attackers from attempting to circumvent the control. This is often because the effort required to circumvent the control is far greater than the potential reward if the attacker is successful, or, conversely, the negative implications of a failed attack (or getting caught) outweigh the benefits of success. For example, by forcing the identification and authentication of a user, service, or application, and all that it implies, the potential for incidents associated with the system is significantly reduced because an attacker will fear association with the incident. If there are no controls for a given access path, the number of incidents and the potential impact become infinite. Controls inherently reduce exposure to risk by applying oversight for a process. This oversight acts as a deterrent, curbing an attacker's appetite in the face of probable repercussions.
The best example of a deterrent control is demonstrated by employees and their propensity to intentionally perform unauthorized functions, leading to unwanted events.
When users begin to understand that by authenticating into a system to perform a function, their activities are logged and monitored, and it reduces the likelihood they will attempt such an action. Many threats are based on the anonymity of the threat agent, and any potential for identification and association with their actions is avoided at all costs.
It is this fundamental reason why access controls are the key target of circumvention by attackers. Deterrents also take the form of potential punishment if users do something unauthorized. For example, if the organization policy specifies that an employee installing an unauthorized wireless access point will be fired, that will determine most employees from installing wireless access points.
Preventative Controls Preventive controls are intended to avoid an incident from occurring. Preventative access controls keep a user from performing some activity or function. Preventative controls differ from deterrent controls in that the control is not optional and cannot (easily) be bypassed. Deterrent controls work on the theory that it is easier to obey the control rather than to risk the consequences of bypassing the control. In other words, the power for action resides with the user (or the attacker). Preventative controls place the power of action with the system, obeying the control is not optional. The only way to bypass the control is to find a flaw in the control's implementation.
Compensating Controls Compensating controls are introduced when the existing capabilities of a system do not support the requirement of a policy. Compensating controls can be technical, procedural, or managerial.
Although an existing system may not support the required controls, there may exist other technology or processes that can supplement the existing environment, closing the gap in controls, meeting policy requirements, and reducing overall risk.
For example, the access control policy may state that the authentication process must be encrypted when performed over the Internet. Adjusting an application to natively support encryption for authentication purposes may be too costly. Secure Socket Layer (SSL), an encryption protocol, can be employed and layered on top of the authentication process to support the policy statement.
Other examples include a separation of duties environment, which offers the capability to isolate certain tasks to compensate for technical limitations in the system and ensure the security of transactions. In addition, management processes, such as authorization, supervision, and administration, can be used to compensate for gaps in the access control environment.
Detective Controls Detective controls warn when something has happened, and are the earliest point in the post-incident timeline. Access controls are a deterrent to threats and can be aggressively utilized to prevent harmful incidents through the application of least privilege. However, the detective nature of access controls can provide significant visibility into the access environment and help organizations manage their access strategy and related security risk.
As mentioned previously, strongly managed access privileges provided to an authenticated user offer the ability to reduce the risk exposure of the enterprise's assets by limiting the capabilities that authenticated user has. However, there are few options to control what a user can perform once privileges are provided. For example, if a user is provided write access to a file and that file is damaged, altered, or otherwise negatively impacted (either deliberately or unintentionally), the use of applied access controls will offer visibility into the transaction. The control environment can be established to log activity regarding the identification, authentication, authorization, and use of privileges on a system.
This can be used to detect the occurrence of errors, the attempts to perform an unauthorized action, or to validate when provided credentials were exercised. The logging system as a detective device provides evidence of actions (both successful and unsuccessful) and tasks that were executed by authorized users.
Corrective Controls When a security incident occurs, elements within the security infrastructure may require corrective actions. Corrective controls are actions that seek to alter the security posture of an environment to correct any deficiencies and return the environment to a secure state. A security incident signals the failure of one or more directive, deterrent, preventative, or compensating controls. The
detective controls may have triggered an alarm or notification, but now the corrective controls must
work to stop the incident in its tracks. Corrective controls can take many forms, all depending on
the particular situation at hand or the particular security failure that needs to be dealt with.
Recovery Controls
Any changes to the access control environment, whether in the face of a security incident or to
offer temporary compensating controls, need to be accurately reinstated and returned to normal
operations. There are several situations that may affect access controls, their applicability, status,
or management.
Events can include system outages, attacks, project changes, technical demands, administrative
gaps, and full-blown disaster situations. For example, if an application is not correctly installed or
deployed, it may adversely affect controls placed on system files or even have default
administrative accounts unknowingly implemented upon install.
Additionally, an employee may be transferred, quit, or be on temporary leave that may affect policy
requirements regarding separation of duties. An attack on systems may have resulted in the
implantation of a Trojan horse program, potentially exposing private user information, such as
credit card information and financial data. In all of these cases, an undesirable situation must be
rectified as quickly as possible and controls returned to normal operations.
The following answers are incorrect:
The other examples are belongs to detective control.
The following reference(s) were/was used to create this question:
CISA Review Manual 2014 Page number 44
and
Official ISC2 CISSP guide 3rd edition Page number 50 and 51
Certification Tracks
Citrix 1Y0-205 is part of following Certification Paths. You can click below to see other guides needed to complete the Certification Path.Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF Include VCE | PDF Include VCE | PDF Include VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | Windows, Android, iOS, Linux | |
Show All Supported Payment Methods
















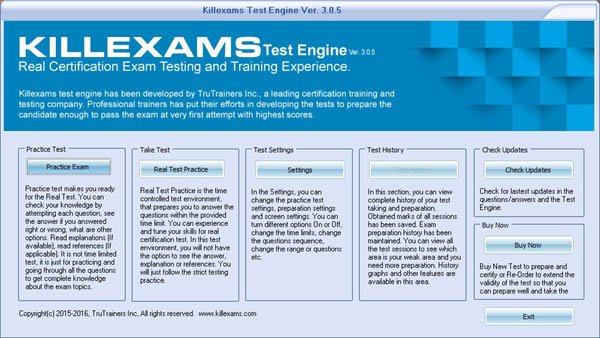
VCE Exam Simulator
Citrix 1Y0-205
Citrix Virtual Apps and Desktops Administration
| VCE Exam Simulator Q&A | : 347 |
| Q&A Update On | : January 3, 2019 |
| File Format | : Installable Setup (.EXE) |
| Windows Compatibility | : Windows 10/8/7/Vista/2000/XP/98 |
| Mac Compatibility | : Through Wine, Virtual Computer, Dual Boot |
| VCE Exam Simulator Software |
VCE Exam Simulator Installation Guide
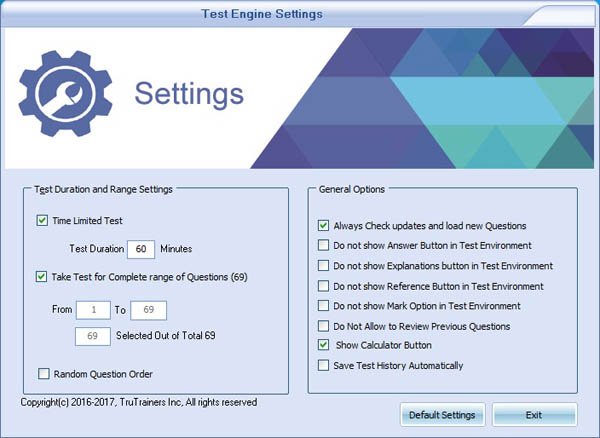
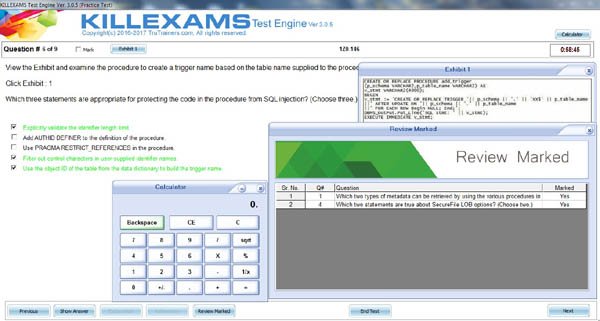
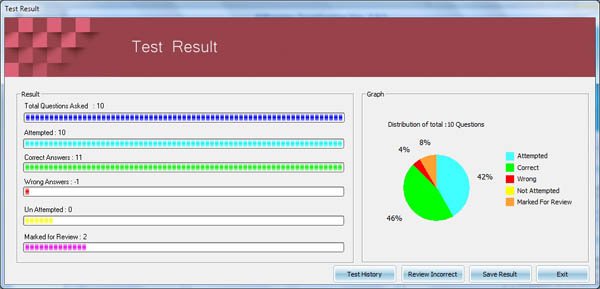
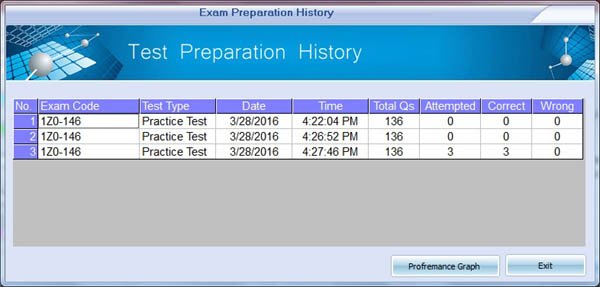
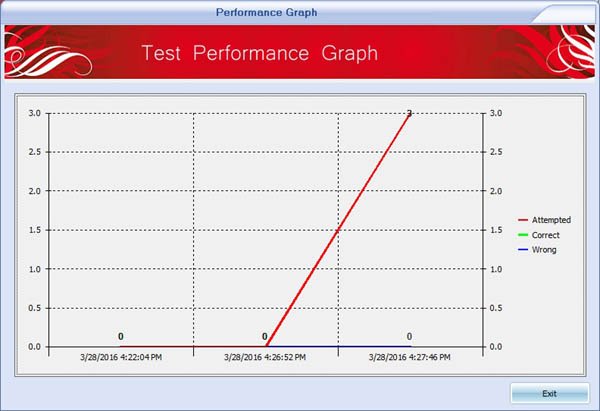
Insideopenoffice Exam Simulator is industry leading Test Preparation and Evaluation Software for 1Y0-205 exam. Through our Exam Simulator we guarantee that when you prepare Citrix 1Y0-205, you will be confident in all the topics of the exam and will be ready to take the exam any time. Our Exam Simulator uses braindumps and real questions to prepare you for exam. Exam Simulator maintains performance records, performance graphs, explanations and references (if provied). Automated test preparation makes much easy to cover complete pool of questions in fastest way possible. Exam Simulators are updated on regular basis so that you can have best test preparation. Pass4sure with Industry Leading Exam Simulator.
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | VCE Include PDF | VCE Include PDF | VCE Include PDF | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
| OS Support | ||||
| OS Support | Windows, Mac (through Wine) | Windows, Mac (through Wine) | Windows, Mac (through Wine) | |
Show All Supported Payment Methods
















Preparation Pack (PDF + Exam Simulator)
Citrix 1Y0-205
Insideopenoffice Preparation Pack contains Pass4sure Real Citrix 1Y0-205 Questions and Answers and Exam Simulator. Insideopenoffice is the competent Exam Preparation and Training company that will help you with current and up-to-date training materials for Citrix Certification Exams. Authentic 1Y0-205 Braindumps and Real Questions are used to prepare you for the exam. 1Y0-205 Exam PDF and Exam Simulator are continuously being reviewed and updated for accuracy by our Citrix test experts. Take the advantage of Insideopenoffice 1Y0-205 authentic and updated Questons and Answers with exam simulator to ensure that you are 100% prepared. We offer special discount on preparation pack. Pass4sure with Real exam Questions and Answers
Preparation Pack Includes
-
Pass4sure PDF
Citrix 1Y0-205 (Citrix Virtual Apps and Desktops Administration)
Questions and Answers : 347 Q&A Update On : January 3, 2019 File Format : PDF Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : All Versions including iOS 4/5/6/7 Android : All Android Versions Linux : All Linux Versions Download 1Y0-205 Sample Questions -
VCE Exam Simulator Software
Citrix 1Y0-205 (Citrix Virtual Apps and Desktops Administration)
VCE Exam Simulator Q&A : 347 Q&A Update On : January 3, 2019 File Format : Installable Setup (.EXE) Windows Compatibility : Windows 10/8/7/Vista/2000/XP/98 Mac Compatibility : Through Wine, Virtual Computer, Dual Boot Download Software VCE Exam Simulator Software Download 1Y0-205 Sample Exam Simulator VCE Exam Simulator Installation Guide
Buy Full Version (Limited time Discount offer)
Compare Price and Packages|
3 Months
Download Account |
6 Months
Download Account |
1 Year
Download Account |
||
|---|---|---|---|---|
| File Format | ||||
| File Format | PDF & VCE | PDF & VCE | PDF & VCE | |
| Instant download Access | ||||
| Instant download Access | ✔ | ✔ | ✔ | |
| Comprehensive Q&A | ||||
| Comprehensive Q&A | ✔ | ✔ | ✔ | |
| Success Rate | ||||
| Success Rate | 98% | 98% | 98% | |
| Real Questions | ||||
| Real Questions | ✔ | ✔ | ✔ | |
| Updated Regularly | ||||
| Updated Regularly | ✔ | ✔ | ✔ | |
| Portable Files | ||||
| Portable Files | ✔ | ✔ | ✔ | |
| Unlimited Download | ||||
| Unlimited Download | ✔ | ✔ | ✔ | |
| 100% Secured | ||||
| 100% Secured | ✔ | ✔ | ✔ | |
| Confidentiality | ||||
| Confidentiality | 100% | 100% | 100% | |
| Success Guarantee | ||||
| Success Guarantee | 100% | 100% | 100% | |
| Any Hidden Cost | ||||
| Any Hidden Cost | $0.00 | $0.00 | $0.00 | |
| Auto Recharge | ||||
| Auto Recharge | No | No | No | |
| Updates Intimation | ||||
| Updates Intimation | by Email | by Email | by Email | |
| Technical Support | ||||
| Technical Support | Free | Free | Free | |
Show All Supported Payment Methods













1Y0-205 Questions and Answers
1Y0-205 Related Links
Customers Feedback about 1Y0-205
"Benedict Says : A few tremendous news is that I exceeded 1Y0-205 check the day past... I thank whole killexams.Com institution. I certainly respect the amazing paintings that you All do... Your schooling cloth is notable. Maintain doing appropriate paintings. I will actually use your product for my next exam. Regards, Emma from the large apple"
"Dingxiang Says : After a few weeks of 1Y0-205 preparation with this Insideopenoffice set, I passed the 1Y0-205 exam. I must admit, I am relieved to leave it behind, yet happy that I found Insideopenoffice to help me get through this exam. The questions and answers they include in the bundle are correct. The answers are right, and the questions have been taken from the real 1Y0-205 exam, and I got them while taking the exam. It made things a lot easier, and I got a score somewhat higher than I had hoped for."
"Christopher Says : I handed the 1Y0-205 exam. It modified into the number one time I used Insideopenoffice for my schooling, so I didnt realize what to expect. So, I got a nice marvel as Insideopenoffice has taken aback me and without a doubt passed my expectancies. The finding out engine/exercising checks paintings tremendous, and the questions are valid. Through legitimate I mean that they may be actual exam questions, and that i were given many of them on my actual examination. Very dependable, and i used to be left with first-rate impressions. Id now not hesitate to propose Insideopenoffice to my colleagues."
"Chandler Says : I handed the 1Y0-205 examination and highly endorse Insideopenoffice to everyone who considers buying their substances. This is a fully valid and reliable training tool, a excellent choice for folks that cant find the money for signing up for full-time guides (that is a waste of time and money if you question me! Especially if you have Insideopenoffice). In case you have been thinking, the questions are actual!"
"Brigham Says : Before I stroll to the sorting out middle, i was so assured approximately my education for the 1Y0-205 examination because of the truth I knew i used to be going to ace it and this confidence came to me after the use of this killexams.Com for my assistance. It is brilliant at supporting college students much like it assisted me and i was capable of get desirable ratings in my 1Y0-205 take a look at."
"Chenglei Says : I spent enough time studying these materials and passed the 1Y0-205 exam. The stuff is good, and whilst those are braindumps, meaning these substances are constructed at the real exam stuff, I dont apprehend folks who try to bitch aboutthe 1Y0-205 questions being exceptional. In my case, now not all questions were one hundred% the equal, but the topics and widespread approach had been surely accurate. So, buddies, if you take a look at tough sufficient youll do just fine."
"Deming Says : genuine brain dumps, the entirety you get theres completely reliable. I heard right reviews on killexams, so i purchasedthis to prepare for my 1Y0-205 examination. everything is as desirable as they promise, exact nice, smooth exerciseexamination. I handed 1Y0-205 with ninety six%."
"Malcolm Says : Just cleared 1Y0-205 exam with top score and have to thank killexams.com for making it possible. I used 1Y0-205 exam simulator as my primary information source and got a solid passing score on the 1Y0-205 exam. Very reliable, Im happy I took a leap of faith purchasing this and trusted killexams. Everything is very professional and reliable. Two thumbs up from me."
"Crosby Says : Great insurance of 1Y0-205 examination principles, so I found out precisely what I wanted in the path of the 1Y0-205 exam. I exceedingly suggest this education from killexams.Com to virtually all and sundry making plans to take the 1Y0-205 exam."
"Chuanli Says : I wanted to inform you that during past in idea that id in no way be able to pass the 1Y0-205 take a look at. however after Itake the 1Y0-205 education then I came to recognise that the online services and material is the quality bro! And when I gave the checks I passed it in first attempt. I informed my pals approximately it, additionally they beginning the 1Y0-205 education shape right here and locating it truely exquisite. Its my pleasant experience ever. thank you"